Russian Hackers Target WhatsApp and Signal: A Growing Threat to Secure Communication
Russia-linked actors are increasingly targeting users of encrypted messaging apps like WhatsApp and Signal in sophisticated phishing campaigns, according to recent warnings from the FBI and cybersecurity agencies. These attacks aren’t breaking the encryption; they’re bypassing it by compromising the users themselves.
The Phishing Tactics: How Hackers Gain Access
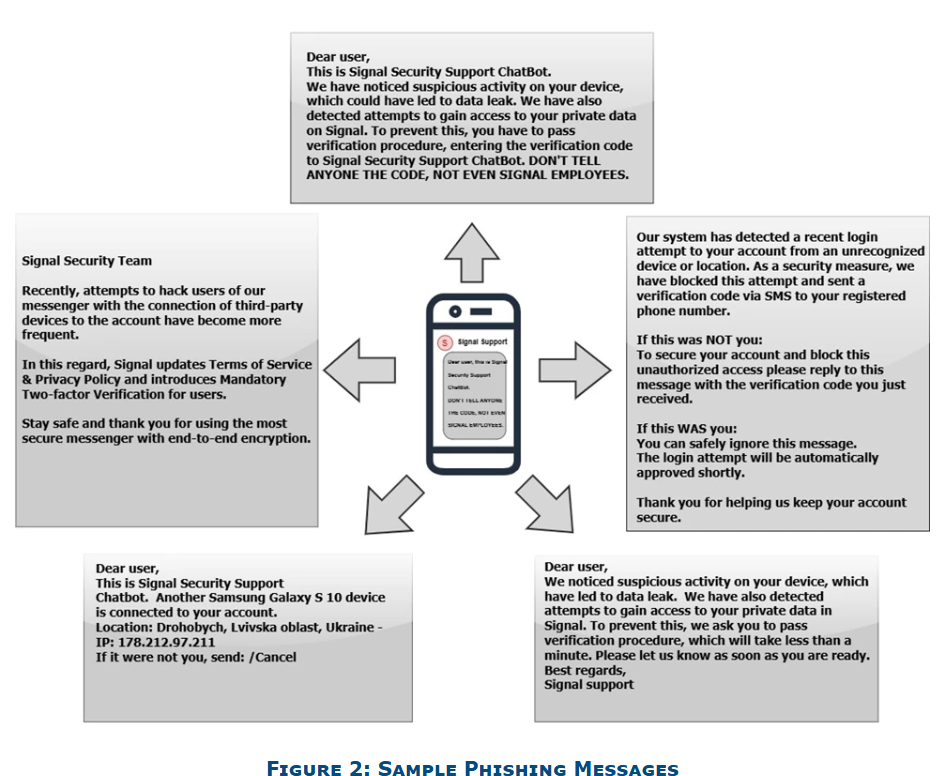
The core tactic involves phishing – tricking individuals into revealing sensitive information. Attackers pose as legitimate support accounts for WhatsApp or Signal, sending tailored messages designed to steal verification codes or PINs. Once obtained, these credentials allow attackers to hijack accounts, gaining access to messages, contacts, and the ability to impersonate victims. The FBI warns that these campaigns specifically target individuals deemed “of high intelligence value,” including current and former government officials, military personnel, political figures, and journalists.
Exploiting Linked Devices
A particularly concerning technique involves exploiting the “linked devices” feature in Signal. Hackers trick users into adding the attacker’s device as a linked device, granting them access to the account. As the campaign evolves, the threat of malware deployment is also increasing, potentially leading to further compromise.
Why Target Encrypted Messaging Apps?
The focus on Signal and WhatsApp is noteworthy. Dutch intelligence agencies (MIVD and AIVD) have highlighted that Russia specifically targets Signal due to its strong end-to-end encryption. The goal isn’t to crack the encryption itself, but to circumvent it by gaining access to the accounts of individuals communicating sensitive information. Officials stress that these apps should not be used for classified or confidential information.
The Global Impact and Scale of the Attacks
These attacks are not limited to a single region. The FBI reports that thousands of accounts worldwide have already been compromised. The campaigns are global in scope, impacting individuals across various sectors and countries. The attacks are particularly concerning as they don’t exploit vulnerabilities within the apps themselves, but rather abuse legitimate features to target individual users.
Protecting Yourself: Staying Vigilant Against Phishing
Protecting yourself requires a heightened sense of vigilance. Here are key steps to take:
- Be Suspicious of Unexpected Messages: Treat any unsolicited message, even from known contacts, with caution.
- Never Share Verification Codes or PINs: Legitimate support teams will never ask for these.
- Verify Links Before Clicking: Hover over links to check the destination URL before clicking.
- Check Group Members: Be aware of who is in your group chats.
- Utilize Security Features: Enable two-factor authentication (2FA) wherever possible.
- Report Suspicious Activity: Immediately report any suspicious activity to the app’s security team or relevant authorities.
Pro Tip: Pause and think before acting on any message that asks for personal information or prompts you to click a link. A moment of hesitation can prevent a significant security breach.
Future Trends: What to Expect
The trend of targeting encrypted messaging apps is likely to continue and evolve. Here’s what experts anticipate:
- Increased Sophistication of Phishing Attacks: Attackers will refine their phishing techniques, making them more convincing and harder to detect.
- Expansion to Other Platforms: While Signal and WhatsApp are current targets, attackers may expand their focus to other encrypted messaging apps.
- Greater Utilize of Malware: The deployment of malware alongside phishing attacks is expected to increase, providing attackers with more control over compromised devices.
- AI-Powered Phishing: Artificial intelligence could be used to personalize phishing messages at scale, making them even more effective.
FAQ
Q: Can these attacks compromise the encryption of WhatsApp and Signal?
A: No, the attacks don’t break the encryption. They bypass it by gaining access to user accounts through phishing.
Q: What is the “linked devices” feature and why is it a risk?
A: The “linked devices” feature allows you to use Signal on multiple devices simultaneously. Attackers can exploit this by tricking you into adding their device, granting them access to your account.
Q: Will app developers fix these vulnerabilities?
A: The issue isn’t a vulnerability in the apps themselves, but rather a social engineering attack targeting users. App developers continue to enhance security features, but user vigilance is crucial.
Did you know? Legitimate app support will *never* ask for your verification code or PIN.
Stay informed about the latest cybersecurity threats and take proactive steps to protect your accounts. Explore additional resources on the FBI’s Internet Crime Complaint Center (IC3) and the Cybersecurity and Infrastructure Security Agency (CISA) websites.