Washington Shifts Cyber Posture Toward Aggressive Defense Amid Global Threats
The White House has issued a new National Cyber Strategy, signaling a decisive pivot toward aggressive defense of U.S. Critical infrastructure. The document outlines a six-pillar framework intended to streamline regulations, modernize federal networks, and deepen collaboration between government and private industry. While administration officials describe the move as a necessary evolution of national security policy, cybersecurity experts warn that the strategy’s success hinges on specific implementation details that remain unclear.
The release comes amid heightened tensions in the digital domain, where state-sponsored actors continue to target energy grids, communication networks, and financial systems. Intelligence assessments have repeatedly flagged persistent campaigns by foreign adversaries to pre-position malware within U.S. Infrastructure. The new strategy aims to counter these threats through a combination of offensive capability development and regulatory reform, though critics argue the plan lacks sufficient specificity regarding the primary actors behind these intrusions.
Identifying the Adversary
A central point of contention among national security analysts is the strategy’s framing of adversary behavior. While the document prioritizes efforts to shape hostile actions in cyberspace, some experts contend it falls short of explicitly naming the states most frequently associated with aggressive campaigns against American networks. Public records from the Cybersecurity and Infrastructure Security Agency (CISA) and the FBI have previously attributed significant infrastructure targeting to state-sponsored groups linked to China, and Russia.

Specific campaigns, such as the Volt Typhoon operation, have been identified by U.S. Authorities as efforts to prepare the battlefield within U.S. Critical infrastructure. Similarly, Russian actors have been observed targeting networking devices to disrupt connectivity. Analysts suggest that without clear identification of these adversaries, diplomatic and defensive measures may lack the precision required to deter future intrusions. Shaping behavior in cyberspace often requires acknowledging the source of the threat to establish accountability.
The distinction matters for international norms. When governments publicly attribute attacks, it sets a precedent for accountability under international law. Ambiguity can sometimes serve diplomatic purposes, but in the context of critical infrastructure protection, clarity allows private sector partners to align their defenses with the most probable threat vectors.
Offensive Capabilities and Private Sector Role
The strategy advocates for the development of offensive cyber capabilities, reflecting a broader shift in how Washington views digital warfare. Recent reports indicate the administration has demonstrated a willingness to utilize these capabilities in response to geopolitical provocations. Though, the proposal to potentially expand the role of private companies in offensive operations has sparked debate within the security community.
While some industry leaders argue for greater agency to “hack back” against attackers, government officials and policy experts caution against relinquishing state control over offensive actions. Allowing private entities to conduct offensive cyber operations introduces significant risks regarding escalation. Conflict in the digital domain can spill over into physical infrastructure or trigger broader geopolitical tensions if not managed through centralized command structures.
The prevailing view among senior analysts is that private sector involvement should remain focused on tool building and network defense. Collaboration is essential, but the actual conduct of offensive operations typically requires the oversight and legal authority reserved for government agencies. This balance ensures that responses are proportional and aligned with broader national security objectives.
Workforce and Institutional Stability
Beyond operational tactics, the strategy emphasizes the demand for a robust cyber workforce. Programs such as CyberCorps: Scholarship for Service are highlighted as critical mechanisms for recruiting talent into government and military roles. These initiatives provide educational funding in exchange for service, helping to address chronic staffing shortages within federal agencies.
Recent fluctuations in federal hiring and budget allocations have posed challenges for maintaining these pipelines. Critics note that workforce development requires consistent funding and clear career pathways. Without a steady influx of skilled personnel, even the most advanced technical architectures cannot be effectively managed. Some experts have called for the establishment of a dedicated military service for cyber operations to better generate and retain specialized talent.
Infrastructure defense also relies on the stability of agencies like CISA. Effective public-private collaboration requires sustained engagement with state and local governments, as well as utility providers. Disruptions to grant programs or advisory councils can weaken the collective defense posture, leaving critical nodes vulnerable to exploitation. Rejuvenating these institutional connections is viewed by many as a prerequisite for securing the grid.
From Strategy to Execution
Strategic documents outline goals, but they lack enforcing power on their own. To translate the six pillars into actionable policy, the administration may need to issue additional executive orders. These orders would task federal agencies with discrete deliverables and establish the organizational constructs necessary for aggressive action against adversaries.
The international community watches these developments closely. U.S. Cyber policy influences global standards for internet governance, data security, and conflict resolution in the digital sphere. Allies often align their own defensive postures with Washington’s lead, while adversaries adjust their tactics based on perceived vulnerabilities. The effectiveness of this new strategy will depend on whether the stated goals are matched by sustained resource allocation and political will.
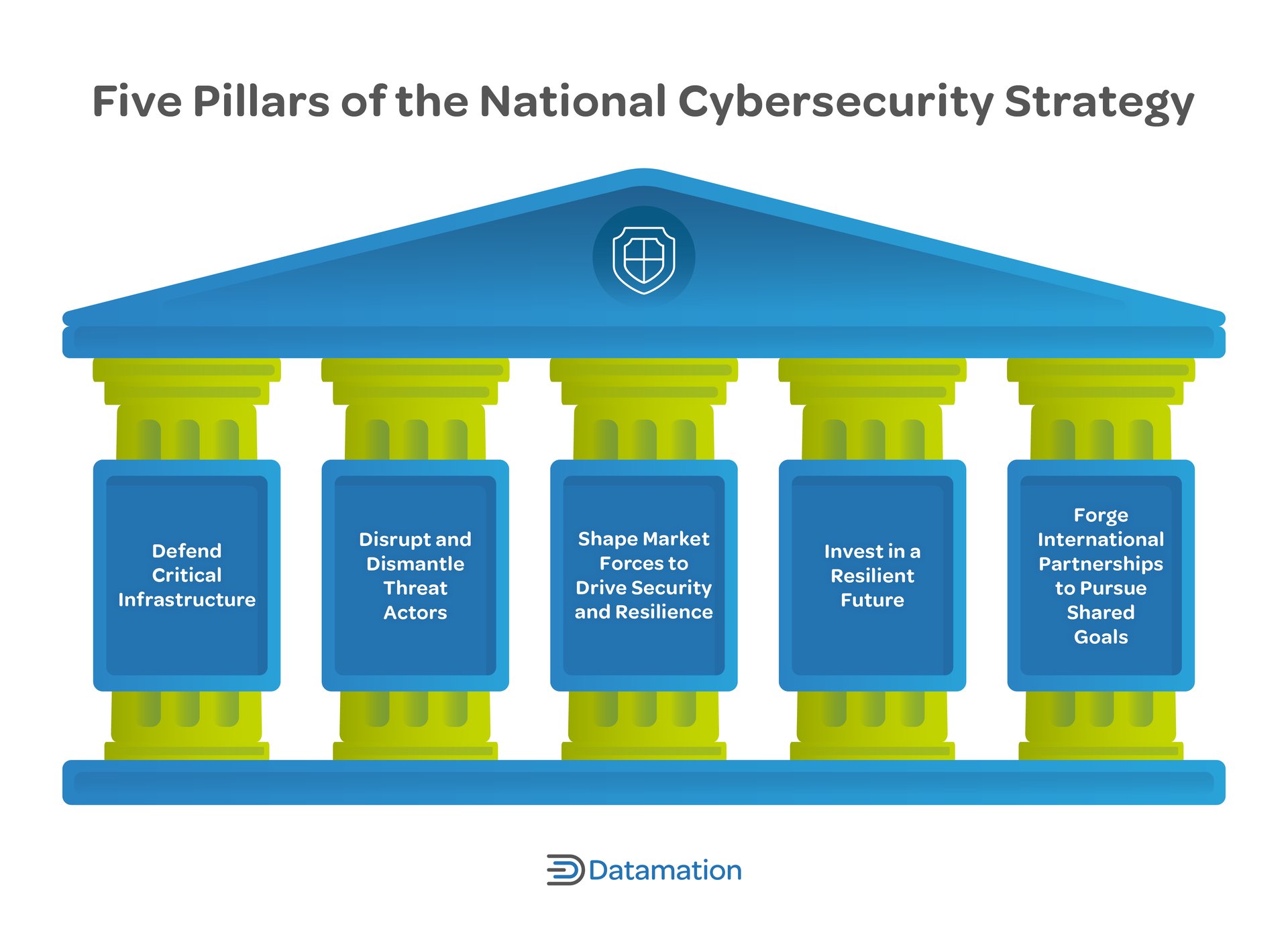
Context: The National Cyber Strategy Framework
The National Cyber Strategy is a comprehensive plan issued by the executive branch to outline the United States’ approach to securing cyberspace. It typically addresses five key pillars: defending critical infrastructure, disrupting and dismantling threat actors, shaping market forces to drive security, investing in a resilient future, and forging international partnerships. Unlike legislation, a strategy document sets policy direction but often requires subsequent executive orders or congressional funding to implement specific measures. Previous iterations have focused on defending forward and imposing costs on malicious actors.
As the administration moves to implement these pillars, the focus will shift to procurement modernization and regulatory streamlining. Technologies such as post-quantum cryptography and zero-trust architecture are cited as essential components for securing federal networks. However, updating legacy systems across a vast bureaucracy takes time and coordination. The transition to cloud computing further complicates this landscape, requiring new safeguards to protect data integrity.
The debate over how best to secure the nation’s digital infrastructure is far from settled. Balancing offensive capabilities with defensive resilience, and government oversight with private sector innovation, remains a complex challenge. As threats evolve, so too must the mechanisms designed to counter them.
How should democracies balance the need for aggressive cyber defense with the risks of escalating conflict in a interconnected global network?