The Quantum Frontier: Stability, Security, and the Race for Computational Supremacy
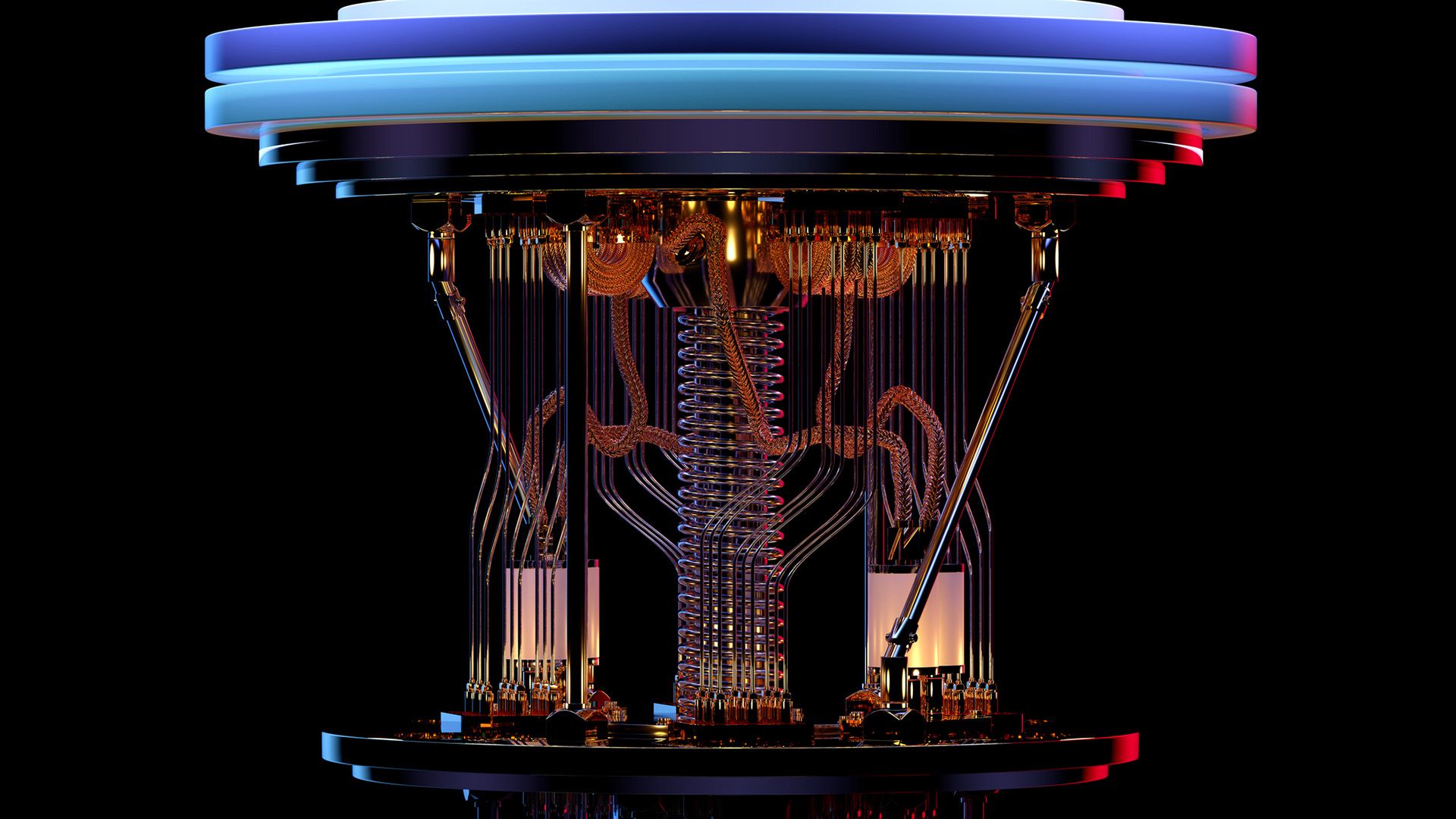
For over a century, Bell Labs has been synonymous with the breakthroughs that define modern life, from the development of solar cells to the Unix operating system. Today, acting as the research arm of Nokia, the organization is pivoting toward a new horizon: quantum computing. While the promise of quantum power is immense, the path to commercial viability is paved with extreme physics and a race against time.
Overcoming the Stability Hurdle: The Rise of Topological Qubits
The primary challenge in quantum computing is the fragility of qubits. Most qubits have a lifespan of typically less than a second, leading to errors and computing failures. To solve this, researchers are exploring “topological qubits.”
Michael Eggleston, a research group leader at Bell Labs and PhD physicist specializing in semiconductor physics and quantum mechanics, compares the topological qubit to a transistor. He notes that it is a “tiny device that’s highly stable,” potentially allowing for advancements that other architectures simply cannot achieve.
Interestingly, different tech giants are taking divergent paths to achieve this stability:
- Nokia’s Approach: Bell Labs utilizes gallium arsenide, a naturally occurring material, to leverage natural processes to create quantum states.
- Microsoft’s Approach: Microsoft has engineered a new state using a combination of superconductors and semiconductors via its Majorana quantum chip.
While Nokia’s current topological quantum computer is experimental—storing a single qubit to perform simple gate processes—it serves as a vital proof of concept for a more stable, multi-qubit future.
Beyond the Hype: Real-World Quantum Applications
Quantum computing isn’t intended to replace the laptop on your desk; rather, it is designed for specific, highly complex calculations that would take classical computers millennia to solve. As the industry moves toward “quantum advantage,” several sectors are poised for disruption.
Simulation and Big Data
The ability to process massive datasets and run complex simulation modeling will revolutionize how we understand molecular structures and system behaviors. This has direct implications for sector-specific drug discovery, where simulating chemical interactions can accelerate the time it takes to bring life-saving medications to market.
Financial Optimization
In the financial world, quantum algorithms could be applied to portfolio optimization, allowing institutions to analyze risk and return variables with a level of precision previously thought impossible.

The Security Crisis: Preparing for ‘Q-Day’
While the computational gains are exciting, there is a darker side to the quantum race: the threat to global encryption. “Q-Day” refers to the point when quantum computers become powerful enough to break existing encryption techniques that protect everything from bank accounts to state secrets.
Governments and security firms are currently in a high-stakes race to establish quantum computers before threat actors do. To counter this, Bell Labs is focusing on post-quantum cryptography. This involves a “security in depth” strategy, which Eggleston describes as layering different protocols and methodologies intelligently rather than relying on a single approach.
Key defensive strategies currently under research include:
- Math-based approaches: Creating encryption algorithms that are resistant to quantum attacks.
- Physics-based approaches: Utilizing quantum key distribution and physical layer key generation to ensure information cannot be intercepted without detection.
The Global Competitive Landscape
The race for quantum supremacy is no longer theoretical; it is a corporate and geopolitical arms race. While Nokia explores topological stability, other players are pushing the boundaries of hardware:
- IBM: Currently targeting “quantum advantage” through hardware advancements, with a goal to achieve this by the end of 2026.
- Google: Moving forward with its own first-party quantum chip, known as Willow.
- Microsoft: Aiming for real-world applications in “years, not decades” via its Majorana chip.
Quantum Computing FAQ
What is decoherence in quantum computing?
Decoherence is the loss of quantum information due to interference from the external environment, which causes qubits to lose their quantum state and leads to computing errors.
What is a topological qubit?
A topological qubit is a more stable type of qubit designed to resist decoherence, acting similarly to a transistor in its ability to provide a reliable foundation for quantum operations.
What is Q-Day?
Q-Day is the hypothetical future date when quantum computers will be capable of breaking the majority of current encryption standards, necessitating a shift to post-quantum cryptography.
Can quantum computers replace classical computers?
No. Quantum computers are specialized tools best suited for complex mathematical problems, big data analysis, and simulations, while classical computers remain superior for general-purpose tasks.
Join the Conversation: Do you believe the threat of Q-Day is being underestimated by modern enterprises, or is the focus on post-quantum cryptography already sufficient? Share your thoughts in the comments below or subscribe to our newsletter for more deep dives into emerging tech.