The Evolution of Boot-Level Security: Beyond the Certificate Cliff
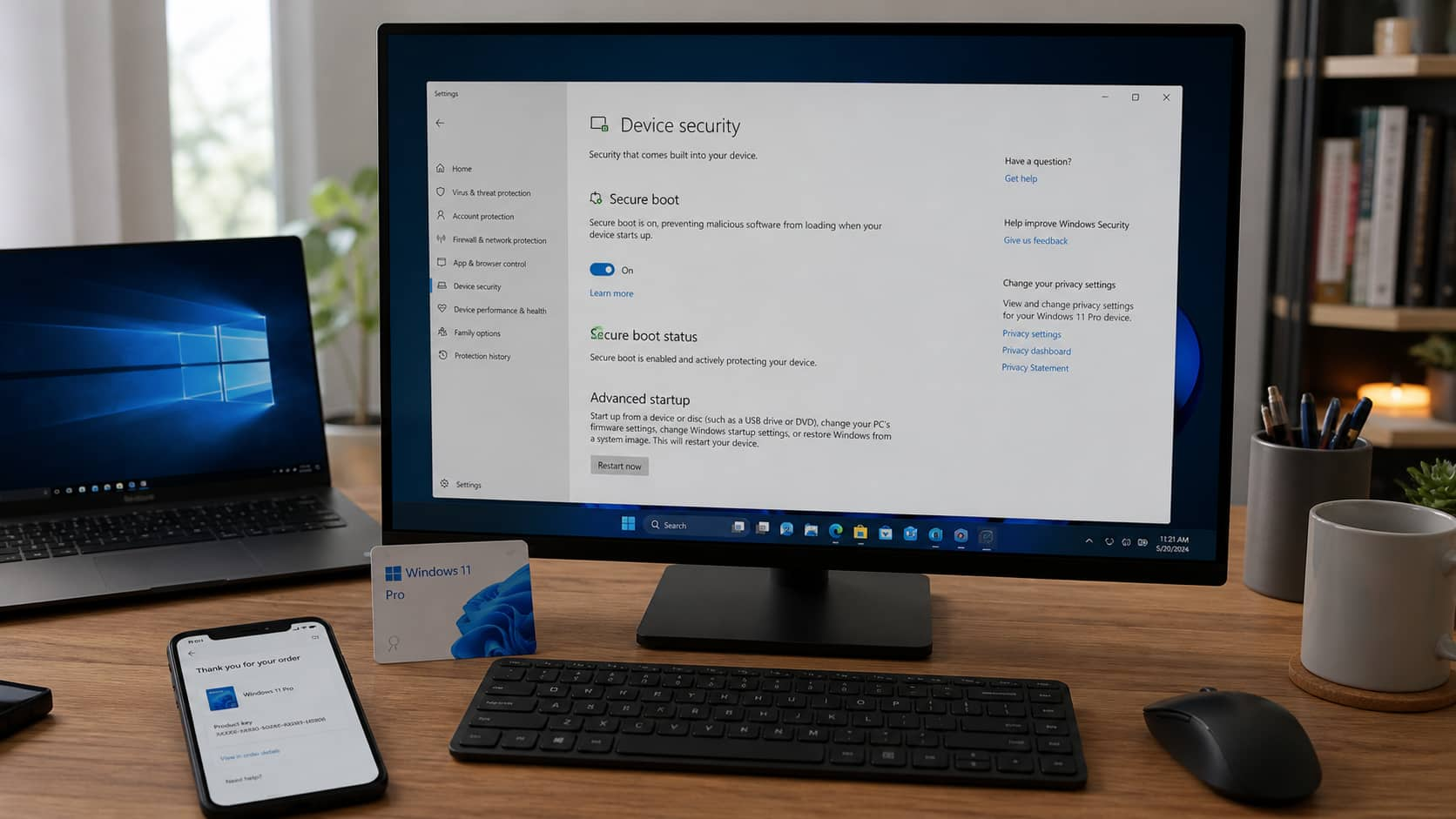
The recent expiration of Microsoft’s 2011 Secure Boot certificates marks a pivotal moment in cybersecurity. For over a decade, the industry relied on a static trust model to ensure that no malicious software could hijack a computer before the operating system even loaded. Yet, as we move deeper into the era of firmware-level attacks, the “set it and forget it” approach to boot security is becoming a liability.
We are witnessing a shift from simple certificate validation to a more dynamic, hardware-rooted security architecture. The goal is to eliminate the “security cliff”—the moment when a massive fleet of devices suddenly becomes vulnerable because a timer ran out.
The Rise of Firmware-Level Warfare
Traditional antivirus software operates within the operating system. But the new frontier of malware, known as bootkits, operates below the OS. A prime example is BlackLotus
, a sophisticated bootkit capable of bypassing Secure Boot and persisting even after a full Windows reinstallation.
Future trends indicate that security will move further into the silicon. We are seeing the integration of technologies like Microsoft Pluton, which embeds security processors directly into the CPU. This reduces the attack surface by removing the communication path between the CPU and the TPM (Trusted Platform Module), where many interception attacks occur.
Forced Obsolescence vs. Security Imperatives
The transition from Windows 10 to Windows 11 highlights a growing tension in the tech industry: the balance between environmental sustainability and cybersecurity. By requiring TPM 2.0 and updated Secure Boot protocols, Microsoft effectively phased out millions of perfectly functional PCs.
Industry analysts suggest a trend toward Modular Security Updates. Instead of requiring a full OS upgrade to patch a boot-level vulnerability, future systems may utilize a decoupled firmware layer that can be updated independently of the primary operating system, extending the usable life of hardware without compromising the user’s safety.
The Shift Toward Zero Trust Architecture at Boot
The industry is moving away from the idea of a trusted boot
(where we trust a certificate) and toward a verified boot
(where every single component is measured and verified against a known solid state in real-time).
In the coming years, expect to observe AI-driven anomaly detection integrated into the UEFI (Unified Extensible Firmware Interface). Instead of just checking if a certificate is valid, the system will analyze the behavior of the boot process. If the boot sequence deviates by even a few milliseconds or accesses an unusual memory address, the system will trigger an automatic lockdown.
Managing the Long-Term Support (LTSC) Paradox
For enterprises, the “expiration cliff” is a nightmare. This represents why versions like Windows 10 Enterprise LTSC 2021 remain critical, as they provide a predictable support window reaching into 2027. However, the trend is shifting toward Continuous Lifecycle Management.
Rather than releasing a version every few years, we are seeing a move toward a “rolling release” model for security certificates. By rotating keys more frequently and automating the distribution via background cloud services, vendors can avoid the systemic risk of a global expiration date.
For more insights on maintaining a secure workstation, explore our guides on optimizing Windows 11 Pro features or securing your home network.
Frequently Asked Questions
What exactly is Secure Boot?
Secure Boot is a security standard developed by members of the PC industry to help make sure that a device boots using only software that is trusted by the Original Equipment Manufacturer (OEM).

Why do security certificates expire?
Certificates expire to force the update of encryption standards. As computing power increases, older encryption methods become easier to crack; expiration ensures that systems move to newer, stronger cryptographic keys.
Can I stay on Windows 10 safely?
Only if you are enrolled in the Extended Security Updates (ESU) program or using an LTSC version. Standard Windows 10 installations without these updates will lack the necessary 2023 certificates, leaving them vulnerable to boot-level threats.
Does Windows 11 fix the certificate issue?
Yes. Windows 11 is designed to handle these updates automatically via Windows Update, ensuring the latest certificates are installed without user intervention.
Is your system ready for the next wave of security?
Share your thoughts in the comments below or subscribe to our newsletter for the latest alerts on firmware vulnerabilities and OS updates.