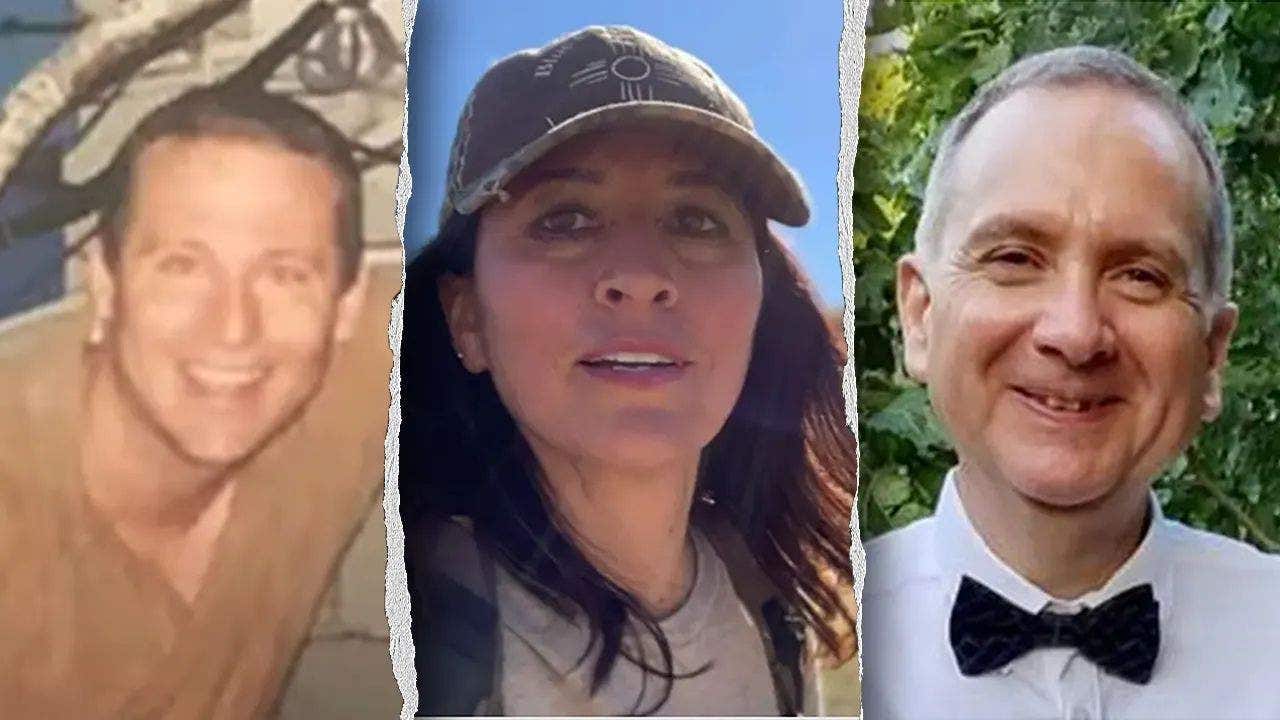
The recent string of disappearances and deaths among top-tier nuclear and space scientists isn’t just a series of tragic coincidences—it’s a flashing red light for global security. When the people holding the keys to the next generation of energy and interstellar travel start vanishing, we aren’t just looking at criminal cases; we’re looking at the frontline of a new, invisible war over intellectual capital.
For decades, the “Cold War” was about missiles and borders. Today, the battlefield has shifted. It’s now about who possesses the specific, nuanced knowledge required to master nuclear fusion, quantum propulsion, and the mysteries of Unidentified Anomalous Phenomena (UAPs). As we move forward, the risks facing high-value scientists will only intensify.
The New Cold War for Intellectual Capital
We are entering an era of “Aggressive Talent Acquisition.” In the past, espionage involved stealing blueprints or hacking servers. While that still happens, the most efficient way to leapfrog a rival nation’s technology is to acquire the mind that created it.
The trend is shifting toward the targeting of “Linchpin Scientists”—individuals whose specific expertise is so rare that their loss or defection could set a national program back by a decade. Whether through coercion, bribery, or more sinister means, the pursuit of these individuals is becoming a primary objective for adversarial intelligence agencies.
The Privatization of State Secrets
One of the most significant trends we’re seeing is the migration of cutting-edge research from government agencies like NASA to private corporations. Companies like SpaceX and Blue Origin are now handling tasks that were once the exclusive domain of the state.
The Security Gap in Private Research
While government facilities have rigorous security protocols and FBI oversight, private firms often operate with more flexibility, which can lead to vulnerabilities. The “corporate campus” environment is far easier to infiltrate than a fortified military base.
As more nuclear and space research moves into the private sector, People can expect a rise in corporate espionage. The line between a “business competitor” and a “foreign agent” is blurring, making scientists in the private sector prime targets for those seeking to bypass government firewalls.
AI and the Precision Targeting of Experts
The days of casting a wide net are over. Artificial Intelligence is now being used to map the “knowledge graph” of an entire industry. By analyzing published papers, patent filings, and conference attendance, AI can identify exactly which scientist holds the missing piece of a technological puzzle.
This allows for “Precision Targeting.” An adversary no longer needs to kidnap a whole team; they only need the one person who understands the specific thermal dynamics of a new reactor or the propulsion physics of a UAP-style craft. This algorithmic approach to espionage makes the “disappearance” of a single, seemingly obscure researcher a strategic victory.
The UAP Paradox: Secrecy vs. Disclosure
The intersection of space science and UAPs adds a layer of volatility. For years, the government maintained a policy of strict denial. Now, with increased congressional pressure and public hearings, the veil is lifting. However, this transition period is the most dangerous time for those “in the know.”
When secrets move from “deep black” programs to the verge of public disclosure, the incentive to silence witnesses or experts peaks. We are likely to see a trend of “strategic leaks” countered by “strategic silences,” where individuals who possess proof of non-human intelligence or breakthrough physics find themselves in the crosshairs of those who believe such knowledge should remain classified for “national stability.”
For more on how government transparency is evolving, check out our analysis on the evolution of government secrecy.
Future Protection Frameworks for High-Value Assets
To counter these threats, we expect a shift in how the U.S. Protects its scientific community. We will likely see the implementation of “Intellectual Asset Protection Programs” that mirror the security provided to high-ranking diplomats.
- Continuous Monitoring: Real-time security audits for scientists working on “Tier 1” technologies.
- Redundant Knowledge Systems: Moving away from “single-point-of-failure” expertise by ensuring critical knowledge is distributed across multiple teams.
- Enhanced Vetting: More rigorous background checks for private contractors handling state-level secrets.
Frequently Asked Questions
Are these disappearances linked to foreign espionage?
While not officially confirmed in every case, the pattern of targeting experts in nuclear and space research strongly suggests a motive of intellectual theft or strategic sabotage.
Why is the FBI involved in scientific deaths?
When a scientist’s work impacts national security, their death or disappearance is treated as a potential intelligence breach rather than a simple local crime.
What is the connection to UAPs?
Some of the affected scientists were reportedly involved in studying Unidentified Anomalous Phenomena, which often involves classified propulsion and materials science that adversarial nations are eager to acquire.
Is the private sector safer than government labs?
Not necessarily. While they have less bureaucracy, private firms often lack the comprehensive counter-intelligence infrastructure that agencies like the Department of Energy provide.
What do you think is happening?
Is this a coordinated effort to stifle scientific breakthrough, or a series of isolated incidents? We want to hear your theories.
Join the conversation in the comments below or subscribe to our National Security newsletter for weekly deep dives.